The moment a nation’s energy supply becomes a silent weapon turned against its own citizens during a sub-zero winter, the boundary between digital code and physical survival evaporates instantly. This guide provides a comprehensive roadmap for understanding and mitigating the risks exposed by the December breach of the Polish renewable grid, which serves as a blueprint for securing modern infrastructure against state-sponsored aggression. By analyzing the strategic failures and necessary reforms, energy providers can learn how to shield critical systems from being weaponized during times of national crisis.
Assessing the Strategic Impact of the Polish Energy Sector Breach
The breach of the Polish energy sector was not a random act of digital vandalism but a calculated strike designed to inflict maximum psychological distress during a period of extreme cold. This incident proved that adversaries no longer prioritize data theft; instead, they focus on systemic paralysis to undermine public trust and national stability. The strike targeted renewable energy infrastructure precisely when the demand for heating was at its peak, demonstrating a chilling evolution in how cyber operations are synchronized with environmental conditions.
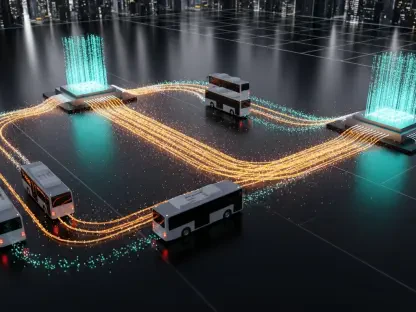
The attack bypassed modern defenses by exploiting the very connectivity that makes smart grids efficient. This analysis reveals that state-sponsored actors are moving toward a model of total disruption, where the goal is to render critical national infrastructure unmanageable from a distance. The chilling implication for global security is that any nation modernizing its grid without equivalent security upgrades is essentially handing a remote kill switch to its adversaries.
The Evolution of Cyber Warfare from Information Theft to Physical Sabotage
The Polish incident represents a sophisticated transition in the threat landscape, moving from traditional IT breaches into the high-stakes realm of Operational Technology disruption. By targeting the intersection of the internet and industrial control systems, attackers demonstrated that wind and solar farms are increasingly susceptible to attacks that remove human oversight. This shift underscores a global emergency where the rush to adopt green technology has inadvertently expanded the attack surface for those looking to weaponize the cold.
This evolution signifies that the era of simple espionage has ended, replaced by an era of digital-to-physical sabotage. Attackers now seek to compromise the specialized hardware that manages energy flow, turning efficiency into a liability. As utilities become more interconnected, the need to protect the physical integrity of the grid becomes just as vital as protecting the data flowing through it.
A Step-by-Step Breakdown of the Attack Chain and Systemic Failure
Step 1: Exploiting Vulnerable Internet-Facing Edge Devices
The initial breach occurred at the network perimeter, where attackers targeted insecure security devices that served as the primary gateway. These FortiGate devices were left exposed to the public internet, providing a direct path for hackers to probe for weaknesses in the external defense layer. This first step highlights how a single poorly configured hardware component can compromise an entire national utility network.
The Critical Risk of Omitting Multifactor Authentication
The absence of Multifactor Authentication allowed attackers to gain entry using simple credential harvesting or brute-force methods. It is now evident that even the most robust security hardware remains a liability if it is not paired with rigorous identity management. Failing to implement MFA essentially left the front door unlocked, proving that single-factor passwords are no longer a viable defense for critical infrastructure.
Step 2: Navigating the Interior via Lateral Movement
Once inside the primary network, the attackers moved horizontally to identify the bridge between general IT systems and the specialized hardware controlling energy flow. This lateral movement was seamless because the internal network lacked proper segmentation, allowing the threat actors to explore the environment without triggering major alarms. Their objective was to find the point where digital commands translated into physical mechanical actions.
The Persistent Danger of Retaining Default Factory Passwords
Attackers easily compromised Operational Technology from major vendors because many systems were still running on out-of-the-box credentials. This catastrophic lack of basic security hygiene allowed the hackers to take full control of the industrial hardware without needing any sophisticated exploits. Retaining default passwords remains one of the most significant and avoidable vulnerabilities in the energy sector today.
Step 3: Executing the “Blinding” Phase through Firmware Corruption
The final stage of the attack was designed to strip operators of their ability to monitor or intervene in the system. Rather than shutting down the power immediately, the hackers focused on a blinding strategy that erased the interface between humans and machines. This created a scenario where the turbines could still be operational, yet the control room was functionally dark and unable to respond to changes.
Deploying Wiper Malware to Erase Human-Machine Interface Data
By deploying wiper malware and corrupting device firmware, the hackers ensured that the grid’s stability remained in a state of unmanaged uncertainty. The destruction of interface data meant that even if the physical equipment was working, the operators had no way to verify the status or safety of the network. This specific tactic shows a move toward long-term sabotage where recovery is hindered by the permanent loss of control data.
Key Technical Takeaways for Critical Infrastructure Protection
- Eradication of Default Credentials: Power providers must enforce mandatory password changes during the initial installation of any industrial control device to prevent unauthorized access.
- Mandatory Firmware Verification: Implementing cryptographic checks ensures that the code running on critical hardware has not been modified or tampered with by external actors.
- Isolation of Edge Devices: Following federal directives to disconnect or rigorously harden any internet-exposed device that cannot support modern security protocols is now a requirement.
- Implementation of MFA Across All Layers: Ensuring that no entry point, regardless of its perceived importance, is accessible through single-factor authentication alone.
Global Implications for the Future of Energy and National Security
The Polish grid hack serves as a precursor to a new era of decentralized energy vulnerability where the transition to renewables introduces thousands of new entry points. As global security bodies like CISA and the NCSC tighten their oversight, the industry must pivot toward secure-by-design principles. The challenge ahead lies in reconciling the need for remote accessibility with the absolute requirement for air-gapped or heavily shielded control systems.
Future developments will likely involve more aggressive federal mandates for private utility providers to meet minimum security benchmarks. The decentralized nature of modern power generation means that a breach at a small wind farm could potentially cascade into a regional crisis. Protecting the grid now requires a collaborative approach that spans across international borders and various sectors of the economy.
Strengthening the Resilience of the Modern Power Grid
To prevent a repeat of the Polish incident, energy providers and national governments treated OT security with the same urgency as traditional military defense. Stakeholders realized that connectivity without rigorous security was a liability that could not be ignored. Organizations that adopted MFA and eliminated default passwords successfully moved from a reactive posture to a proactive defense. These entities prioritized firmware integrity and audited their infrastructure to implement the secure-by-design standards necessary for public safety. Ultimately, the industry shifted toward automated threat response systems that protected the public from the next generation of digital-to-physical threats.